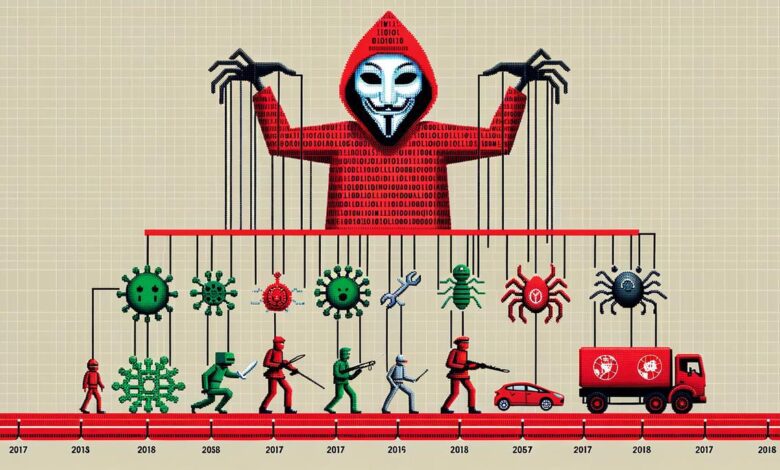
In the ever-shifting digital landscape, the specter of cyber threats looms large, casting shadows that evolve and grow more complex with each technological advancement. The journey from the inception of simple computer viruses to the machinations of state-sponsored cyber warfare marks a daunting trajectory that underscores the urgent need for robust cyber defenses. As we thread through the annals of digital combat, it becomes clear that the battleground is not solely within the circuitry and codes but also woven into the very fabric of human interaction and global dynamics. This essay endeavors to dissect these multifaceted challenges and illuminate the path towards a fortified cyberspace through an intricate tapestry of history, best practices, human factors, emerging technologies, and international collaboration.
The Evolution of Cyber Threats
How Cyber Threats Have Advanced with Technology
In the rapidly expanding digital cosmos, cyber threats have metastasized alongside technological advancements—a relentless parallel progression. The pace at which technology advances obliges the cybersecurity field to perpetually adapt and confront increasingly sophisticated threats. Understanding the transformation of these digital risks is essential to safeguarding our interconnected society.
Initially, cyber threats were rudimentary in form, often amounting to nothing more than digital pranks. They typically exploited basic vulnerabilities in systems that were less complex and comparatively unprotected. Notorious examples include the creation and distribution of simple viruses, which were primarily designed to annoy rather than to inflict severe damage.
As global reliance on the internet burgeoned, so did the complexity of cyber threats. The dawning of the internet age expanded the playground for malicious actors. With the proliferation of personal computers, cybercriminals began orchestrating more serious offenses, such as deploying worms that could independently replicate and traverse networks, wreaking havoc on a larger scale.
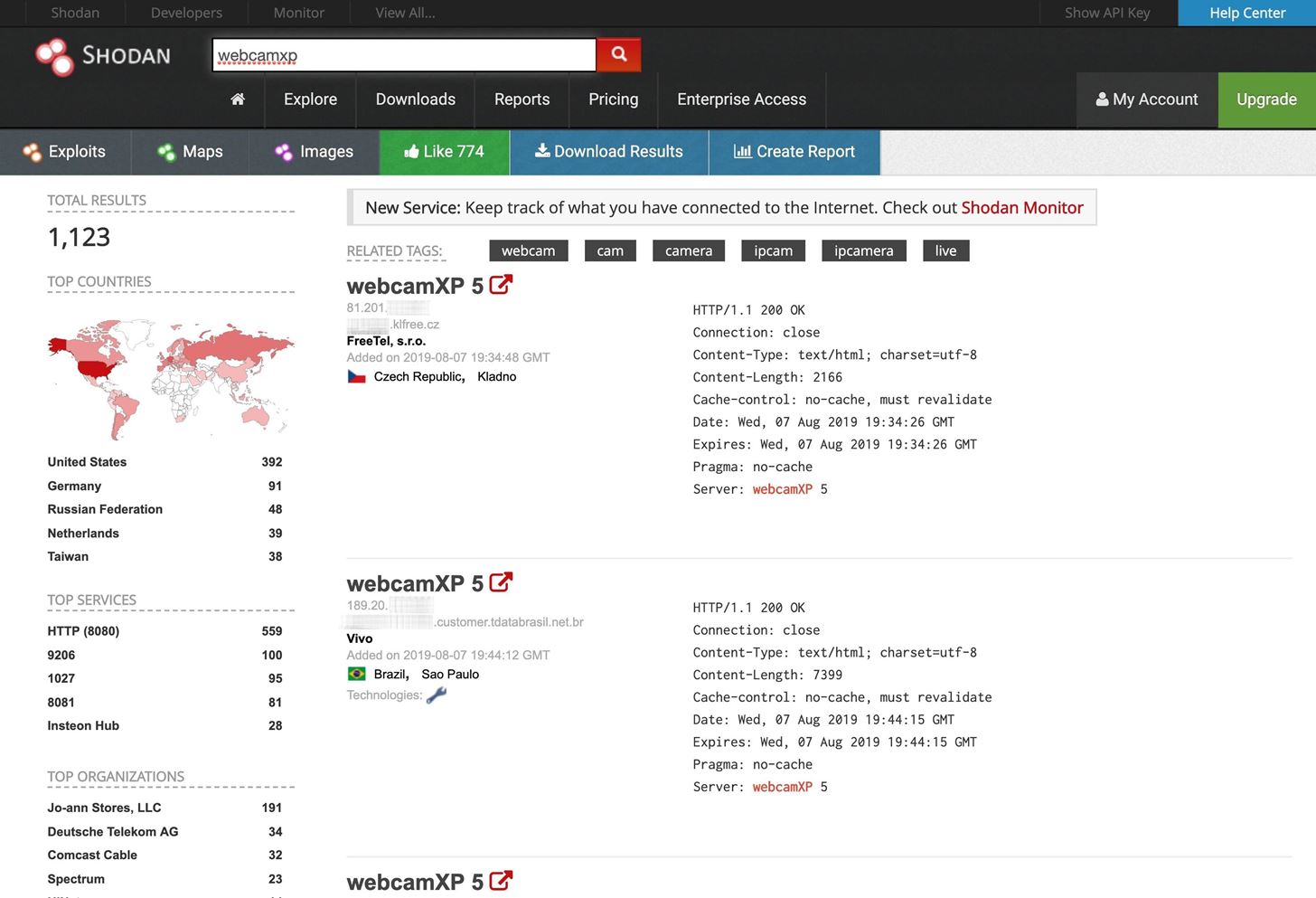
In the present digital epoch, the advancements in technology have carved a dual-edged sword—ushering in conveniences and threats with equal vigor. The proliferation of smart devices and the expansion of the Internet of Things (IoT) have introduced a multitude of potential vulnerabilities. Cyber threats are no longer limited to personal computers but can target any device that connects to the internet: fridges and cars, to industrial control systems.
One illustrative leap in the evolution of cyber threats has been the sophistication of attack vectors. Phishing—frauds that deceive individuals into divulging sensitive information—has advanced from crudely composed emails to compellingly personalized messages through social engineering. This technique manipulates human psychology, exploiting trust to breach secure environments.
Moreover, the rise of big data and machine learning technologies has granted cyber offenders the tools to automate and optimize their attacks. Algorithms can now identify patterns, automate the exploitation of vulnerabilities, and conduct attacks on a monumental scale with chilling precision.
Among the most formidable modern cyber threats includes ransomware. These malicious programs encrypt an individual or organization’s data, holding it hostage until a ransom is paid. Notoriously, ransomware can paralyze critical infrastructure, as demonstrated by attacks on healthcare systems and municipal services.
Finally, state-sponsored cyber warfare poses a significant threat to global security. Nations now have divisions dedicated to launching and defending against cyber operations that can disrupt critical infrastructure, steal intellectual property, and even influence elections.
In conclusion, technological advancements have profoundly impacted the landscape of cyber threats, imbuing them with unwelcome complexity and power. Such threats now demand unceasing vigilance and innovative countermeasures to protect our increasingly digital world. The responsibility falls upon the cybersecurity community to thwart these pernicious threats and preserve the integrity of our cyberspace. Without constant effort and adaptation, the balance tips in favor of those who wish to do harm through the ether of our interconnected existence.

Cybersecurity Frameworks and Best Practices
The continual surge in cyber threats necessitates robust cybersecurity frameworks that are capable of guiding enterprise efforts to shield assets and data. Well-articulated cybersecurity guidelines are pivotal for organizations to maintain the integrity, confidentiality, and availability of their digital resources. Among the most prominent frameworks that underpin the strategies for enterprise defense are:
1. ISO/IEC 27001:
One notable standard is the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC) 27001. This global benchmark provides a comprehensive set of requirements for an information security management system (ISMS). The protocol empowers organizations to manage the security of assets such as financial information, intellectual property, employee details, and information entrusted by third parties.
2. NIST Cybersecurity Framework:
The National Institute of Standards and Technology (NIST) Cybersecurity Framework is a voluntary framework consisting of standards, guidelines, and best practices to manage cybersecurity-related risk. The framework’s core consists of five concurrent and continuous functions — Identify, Protect, Detect, Respond, Recover. This allows organizations a high-level, strategic view of the lifecycle of managing cybersecurity risk.
3. CIS Controls:
The Center for Internet Security (CIS) Controls presents a prioritized set of actions to protect organizations and data from known cyber attack vectors. The CIS Controls are designed to be accessible for organizations of any size and in any sector. They offer a concise, actionable checklist that encapsulates many of the smart practices for cybersecurity.
4. PCI DSS:
For organizations that handle credit card transactions, the Payment Card Industry Data Security Standard (PCI DSS) is a key framework. It requires that both the merchants and service providers that store, process, or transmit credit card data maintain a secure environment, ultimately protecting cardholder data from fraud and theft.
5. GDPR:
On an international scale, the General Data Protection Regulation (GDPR) reshapes the way in which sectors manage data protection. While being a legal framework from the European Union, it imposes obligations onto organizations anywhere, so long as they target or collect data related to people in the EU.
6. Cyber Resilience Framework:
This framework takes into account not only the prevention of cyber attacks but also the ability of an organization to continue operating during an attack and to recover afterwards. It integrates cybersecurity with business continuity management, ensuring that organizations are able to withstand cyber incidents and maintain essential functions.
7. Zero Trust Model:
A strategic initiative that helps prevent successful data breaches by eliminating the concept of trust from an organization’s network architecture. The Zero Trust model is based on the principle “never trust, always verify,” which means continuous monitoring and validation of the security posture of all devices, users, and infrastructure components.
Each of these frameworks serves as a template from which an organization’s specific policies, procedures, and protocols can be crafted. Tailoring these frameworks to the unique needs and risk exposure of an enterprise ensures that cybersecurity efforts are both effective and efficient. It allows for the deployment of a tailored defense, pivotal in the overarching cybersecurity strategy.
Adopting and adapting to these frameworks requires a dynamic approach to stay aligned with the evolving threat landscape. The intersection of robust cybersecurity frameworks and the implementation of adaptive, proactive, and strategic cybersecurity practices provides enterprises with the best possible defense against the multitude of cyber threats faced today. With the cybersecurity landscape constantly changing, these frameworks evolve, adapting to incorporate the latest technology and counter new forms of attacks, representing a cyclic and enduring commitment to digital safety and security.

Human Factors in Cybersecurity
Human factors play a monumental role in both exacerbating and mitigating cyber threats, a dichotomy that requires attention for comprehensive cybersecurity strategies. On one hand, humans can be the weakest link in the cyber defense chain; on the other, they are also the most adaptable and creative asset in the fight against cybercrime.
The phenomenon of "social hacking" illustrates how human psychology can be exploited. By manipulating human behavior, cybercriminals often bypass sophisticated technical defenses. This manipulation exploits traits such as trust, fear, curiosity, and unwitting complacency. The human penchant for error, such as the setting of weak passwords or the mismanagement of sensitive information, further invites risk.
Conversely, the human capacity for critical thinking and adaptation is pivotal in identifying and responding to novel threats. Cybersecurity professionals train to anticipate the patterns and tactics of adversaries, often employing behavioral analytics to predict and counteract intrusions. Humans are well-placed to interpret context—a task that purely automated systems can misjudge, leading to either an oversight in defense or an overzealous response that may impede legitimate activities.
Moreover, cybersecurity awareness training is paramount in cultivating a culture of security. By educating employees on best practices and potential risks, organizations fortify their first line of defense—their own personnel. Humans adept at recognizing phishing attempts or suspicious behavior can prevent breaches from materializing.
User interface and experience design also play a role in defending against cyber threats. By creating systems that are not only secure by default but also user-friendly, designers reduce the chance of human error. Design considerations that take into account common user behaviors can mitigate risks associated with poorly designed systems that might otherwise lead to security lapses.
In the context of safeguarding critical infrastructure and sensitive data, legislative and policy frameworks require a human-centric approach. The establishment of regulations and guidelines for cybersecurity practices necessitates a deep understanding of human factors and behaviors. Beyond compliance, a robust ethical framework also relies on a human touch to ensure the respect of privacy and civil liberties in the digital realm.
Strategies such as the adoption of the Zero Trust Model encapsulate the central role humans play in cybersecurity. Zero Trust operates under the assumption that trust is a vulnerability. By verifying every request as if it originates from an open network, this model recognizes that human error or malicious intent could exist internally as well as externally. Such a strategy is effective because it addresses the inherently unpredictable nature of human behavior.
In conclusion, human-centered approaches remain integral to the cybersecurity landscape. The interplay between human behavior and technological systems must be continuously studied and understood in order to stay ahead of cybercriminals. Crafting cybersecurity defenses that leverage human strengths and counteract human vulnerabilities is vital to prevailing in an ever-evolving digital battleground.

Emerging Cybersecurity Technologies
Emerging Technologies Shaping Cybersecurity’s Future
In the dynamic field of cybersecurity, emerging technologies play a crucial role in fortifying digital defenses and countering incessant threats. As the framework for potential solutions evolves, it is imperative to examine technologies that are influential in shaping the future landscape of cybersecurity.
One such technology is artificial intelligence (AI), transcending its previous applications to become a formidable force against cybercrime. AI systems are proficient in the rapid identification of new threats by analyzing patterns and anomalies with remarkable speed and efficiency. Through the instantiation of complex algorithms, these systems provide preemptive security measures, effectively enhancing threat detection and response capabilities beyond human speed.
Quantum computing is poised to revolutionize the cryptographic infrastructure that currently protects data. The sheer computational power of quantum computers presents both a challenge and an opportunity. While there is a potential risk to encryption methods today, the advent of quantum-resistant algorithms offers a resilient cryptographic paradigm. This quantum-safe cryptography aims to secure data against future threats birthed from quantum advancements.
Blockchain technology, most notable for its application within the realm of cryptocurrencies, stands as a bastion for secure and transparent transactions. Its decentralized and immutable ledger system is resistant to tampering and revision, ensuring the integrity of transactional data and digital assets. Blockchain’s potential extends into the establishment of secure communication channels that are particularly resistant against common cyber threats like data breaches and identity theft.
Another burgeoning area with significant implications for cybersecurity is the development of advanced endpoint detection and response (EDR) systems. EDR solutions proactively safeguard endpoints – such as mobile devices, computers, and servers – by continuously monitoring and analyzing data for signs of cyber threats. These systems not only detect incidents but also analyze them and recommend appropriate actions to mitigate the threat, substantially reducing the time between intrusion detection and response.
The interconnectedness of devices and software platforms has prompted the evolution of security orchestration, automation, and response (SOAR) tools. SOAR platforms integrate disparate security systems and automate responses to cyber incidents, providing a more coordinated and agile defense mechanism. In the swiftly changing landscape of digital threats, SOAR tools aid in the elimination of silos between security teams and technologies, thereby streamlining the incident response processes.
Lastly, with the proliferation of cloud services and the decentralization of data storage and processing, cloud security posture management (CSPM) technologies have come to the forefront. CSPM systems provide continuous monitoring and compliance assurance for cloud environments, preventing misconfigurations and gaps in security practices that could lead to data breaches.
The trajectory of cybersecurity is inexorably linked to these emerging technologies. Each advancement, each new tool, contributes to the robust fabric of digital security measures protecting information in the modern era. As we forge ahead into an evermore connected world, it is incumbent upon cybersecurity professionals to remain heedful of these technologies, integrating them into comprehensive defense strategies that secure the digital realm against the adversaries of tomorrow.
The Global Cybersecurity Ecosystem
International Collaboration as a Keystone in Fortifying Global Cybersecurity
In an era where cyber threats transcend borders, international collaboration stands as a pillar of global cybersecurity. This pivotal interaction among nations, corporations, and entities plays a crucial role in constructing a resilient defense against rampant cybercriminal activities that no single entity could tackle in isolation. Firstly, international collaboration engenders the sharing of threat intelligence, which is vital for preemptive cybersecurity measures. By exchanging information about new threats and vulnerabilities, countries and organizations can collectively develop strategies to mitigate these risks before they escalate into global problems. Cybersecurity exercises and joint response efforts are another facet of international cooperation. These exercises, which often simulate cross-border cyber incidents, help participants refine incident response protocols, enhance technical capabilities, and improve coordination mechanisms. In the crucible of these simulated crises, stakeholders forge the bonds necessary for effective real-world collaboration. Moreover, international partnerships facilitate the harmonization of cybersecurity standards and policies. Uniformity in cyber policies not only reduces friction in international commerce and communication but also ensures a consistent approach to securing critical infrastructure. This can be particularly impactful in sectors such as finance and healthcare, where data breaches can have catastrophic consequences. The fostering of a global cybersecurity workforce through educational and professional exchange programs is an additional merit of international collaboration. By tapping into diverse pools of expertise and fostering cross-cultural academic research, the quality and innovation in cybersecurity practices are significantly augmented. International legal cooperation is essential for combating cybercrime, as it helps bridge the gaps in jurisdictions that cybercriminals often exploit. Global treaties and agreements, alongside respective law enforcement agencies’ collaboration, pave the way for swift and effective legal action across different territories. Lastly, collaboration helps in establishing a more equitable cybersecurity landscape, where resources and knowledge are shared to elevate nations with weaker cyber defenses. This aspect of international solidarity not only strengthens individual countries but collectively enhances global cyber resilience against asymmetric threats. Global cybersecurity is not a zero-sum game; rather, it thrives on the foundational premise of shared security. International collaboration is a linchpin in this endeavor, equipped to build a collective defense that is far more robust than any siloed attempt to protect against the nefarious elements of the digital age.